The latest reports indicate WannaCry ransomware remains a creeping threat with around 200,000 of reported system infections around the world. Online security experts have estimated that the attack, rumored to have been deployed from North Korea, swiftly swept through 150 countries and counting.
And according to BGR, the spread of WannaCry wasn't halted at all, contrary to earlier reports. The Trojan virus was merely slowed down but it remains actively spreading.
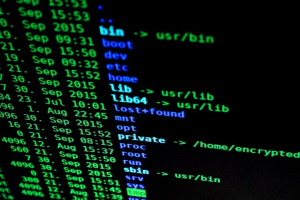
Designed as a ransomware, WannaCry attacks a system by taking control or hijacking a system and this is done by encrypting users' files, thus leaving victims helpless. Owners of infected systems are then advised to pay up to recover their files, which will be decrypted using an application that only the attackers can provide.
Payment starts at $300, which can be coursed through at a bitcoin address provided to victims, who were given three days to send out the ransom money. Failure to do so will mean the ransom will be doubled. And those who refused to fork out $600 in bitcoin payment after seven days, "WannaCry will delete all of the encrypted files and all data will be lost," BGR reported.
According to web security experts, WannaCry is so sophisticated that it can encrypt nearly all known file extensions. That's like saying, nothing and no one is immune from the WannaCry infection.
But most vulnerable are PC users with the outdated operating system, specifically Windows XP, Windows Server 2003 and Windows 8. As Microsoft no longer provides support for these obsolete OS versions, the systems they run are virtually inviting WannaCry with arms wide open.
For Windows 10 users, a critical patch has been deployed by Microsoft engineers to deal with the attack and it goes without saying that downloading and installing the update is an absolute must.
Users can also bolster their security by using security suite - anti-virus, anti-malware, and firewall - and making sure that the tools are updated. No need to worry that money is needed for such protection as free solutions are readily available on the web. Some of the more prominent brands to take note of are Avast, AVG, Comodo and Malwarebytes Anti-Malware.
The latter can be used in tandem with existing anti-virus and firewall application, which will offer an extra layer of robust security.
Experts, however, concede that WannaCry, with help from unsuspecting users, can bypass these protective shells and still grab control of targeted systems, which when infected will mean the end-game.
As of writing, cyber security experts are still figuring out how to unlock the decrypted files on affected systems but no luck. "No means of third-party decryption are available right now," according to BGR.
But users prudent enough to make a backup of their files through an external storage can recover from the episode by going offline, unplugging everything and start over, that is reset their PC and then restore everything from scratch. Luckily, in this case, they can simply ignore the WannaCry ransom demands.
For the unlucky ones, with no backup files to go to, the only clear option is to pay up and cross their fingers that the attackers will actually return their files.